Targetted Training on Advanced Side Channel Evaluation of Hardware Security (ASCEHS)
Date: July 2 nd to July 6 th , 2018
Venue: Maitryee Auditorium, IIT Kharagpur
Motivation
To develop the framework and evaluation criterion for security evaluation of IT products is of utmost requirement. In the recent past various types of side channel attacks have been published into the literature and it has been demonstrated that they can be very effectively used to breach the security of IT products. Some of the attacks like Power Attack, EM Attack, Timing Attack (Including Cache attacks), Fault Attack, Acoustic Attack, Row Hammer Attack and Spectre/Meltdown Attack published recently have really changed the way security evaluation of IT products are carried out. In this proposed targeted training, our endeavour is to have deep understanding of these attacks leading to development of strong evaluation criterion for Side Channel Evaluation of IT products.
Course Content
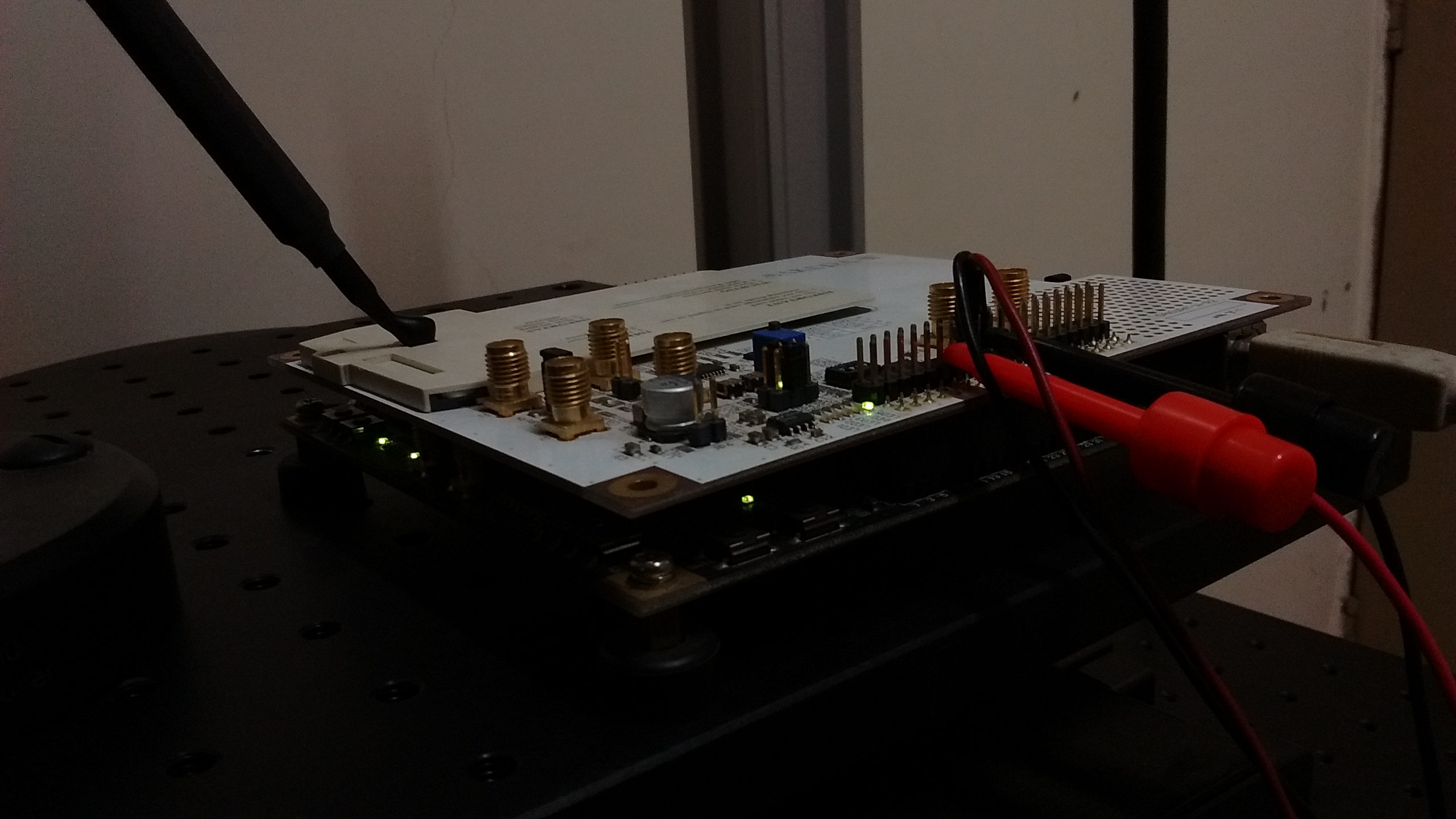
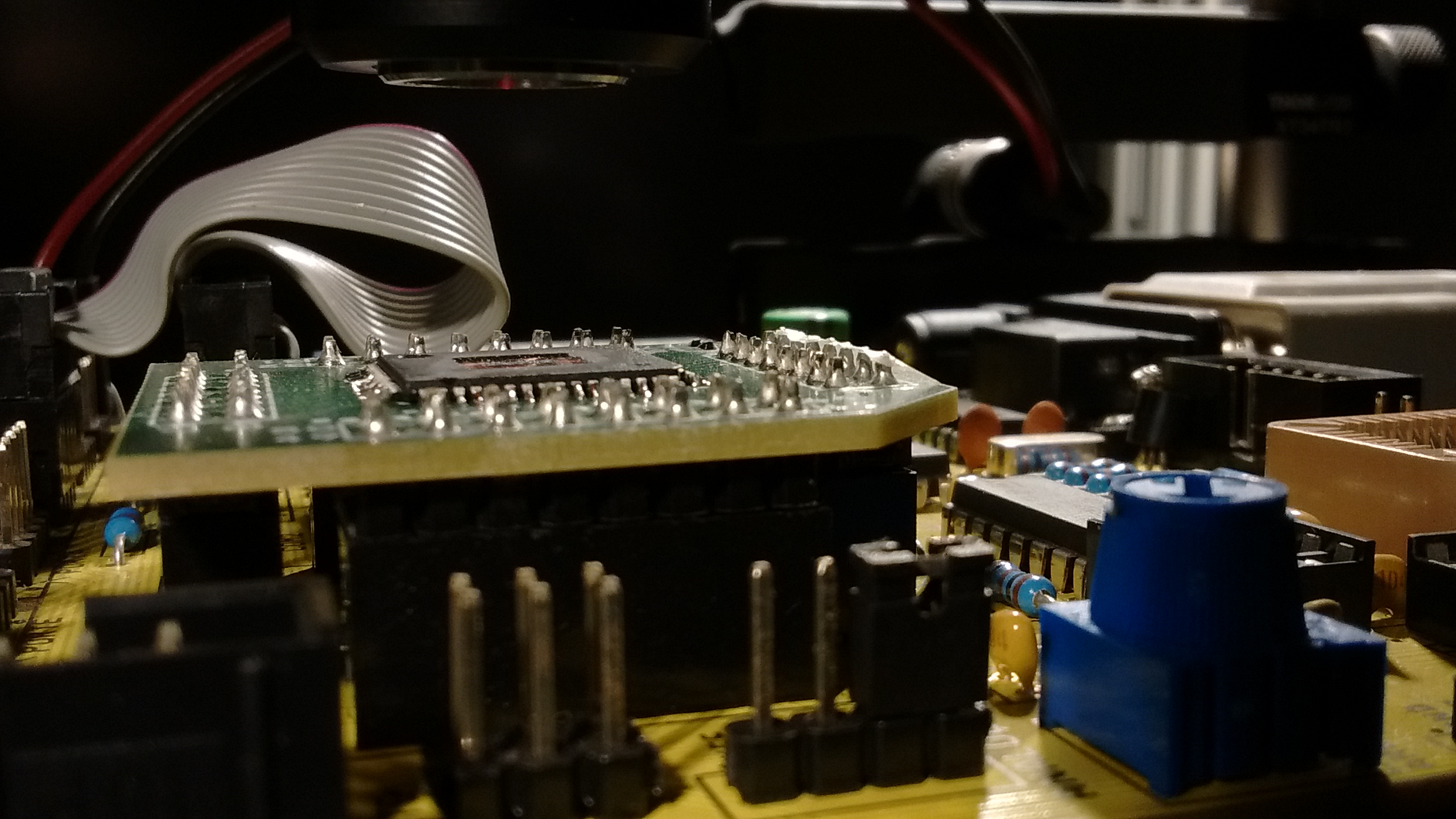
There has been tremendous advancements in side channel attacks. With the development of attacks like Spectre and Meltdown, it becomes imperative that these avenues of leakage of secret cannot be neglected. Otherwise it can lead to catastrophic consequences. In this targeted training, we attempt to bring in one common platform leading experts from international academia and industry, who has produced ingenious attacks and mitigation techniques. The speakers are carefully chosen to cover the thrust areas, ranging from side channels on embedded platforms to micro- architectures affecting the personal computers and laptops. In addition, we also envisage to add talks on usage of machine learning for early side channel detections and side channels on some chosen post- quantum cryptographic implementations. The targeted training would also be assisted with suitable practical demonstrations to make the theory more understandable.
Schedule

SECURE-IC Training (Day 5 – July 6th, 2018)
Evaluating Security during IC-Design – Use Cases
Learn advanced analysis methods with Secure-IC experts, using Analyzr™, Virtualyzr™ and Catalyzr™ tools.
 |
Program:
Venue: |
More information on the One-day Tutorial Workshop offered by Secure-IC is available on the external partner website.
Download the information flyer here.
Course Outline
In this proposed targeted training, we propose the following tentative program. We have got tentative
approvals from the following speakers. In addition, the targeted training will also consist of talks from
Indian faculty members and research scholars, with expertise in Side Channel Analysis.
| S.NO | Speaker | University | Title/Topic |
|---|---|---|---|
| 1 | Sylvain Guilley | TelecomParis, France Secure-IC, France | Side Channel Analysis |
| 2 | Benedikt Gierlichs | K U Leuven, Belgium | Power Analysis |
| 3 | Shivam Bhasin | NTU Singapore | Advanced Physical Attacks on Embedded Systems and Beyond |
| 4 | Jakub Brier | NT U Singapore | Fault Analysis On Assembly |
| 5 | Avi Mendelsen | Tel Aviv, Israel | Micro Architectural Attacks |
| 6 | Yuval Yarom | Adelaide Univ, Australia | Spectre/Meltdown/Microarchitectural Analysis |
| 7 | Subidh Ali | IIT Bhilai | Scan Chain Attack |
| 8 | Debdeep Mukhopadhyay | IIT Kharagpur | Fault Attacks Automation |
| 8 | Sarani Bhattacharya | IIT Kharagpur | Branch Predictor Attacks HPCs |
| 9 | Debapriya Basu Roy | IIT Kharagpur | 1) Implementation Aspects and Fault Vulnerability PQ Candidate - SIKE
2) From TVLA to Success Rate: New Paradigm for Side-Channel Vulnerability Detection |
| 10 | Manaar Alam | IIT Kharagpur | Early detection of Anomaly using Side-Channel: Statistics and Learning |
| 11 | Sayandeep Saha | IIT Kharagpur | ExpFault: Automated Framework for fault Characterization |